
Decisive (but targeted, non-ubiquitous) voting fraud occurred on November 3, 2020. What follows is an explanation and the evidence behind it.
- Starting in 1997, Smartmatic systems were developed in Venezuela with built-in functionality permitting precinct administrators to override security features it appeared to incorporate. Among the extraordinary privileges it gave administrators were abilities to:
- shave votes continuously from one candidate to another;
- batch ballots for later “adjudication” but which instead became a pool of votes that the administrator could simply assign to the candidate of choice;
- generate blank ballots.
- Through a series of licensing agreements, bankruptcies, and corporate mergers and acquisitions, that code ended up in various US election systems (e.g., Dominion, ES&S) which (branding aside) still derive from Smartmatic (a.k.a. Sequoia). Thus, they brought to US elections not only the generous functionalities permitting manipulation by administrators, but porous security, extending such powers to those abroad.[i]
- Since 2006 the fact that systems developed for Hugo Chavez were managing any US elections began striking some prescient Americans as unfortunate.[ii] Their trepidation was well-placed: on November 3, 2020 those systems were used strategically & aggressively to rig our election.
- It was strategic in that it was not “widespread” but targeted at six locations[iii] which, if flipped, also would flip the swing states in which they are found (and thus, the electoral college);
- It was aggressive for the simple reason that Trump broke their algorithm, because he was on his way to a win that exceeded their ability to overcome through minor cheats alone. It is for that reason that in those six locations the bad guys went full-on-goon (e.g., thugs intimidating observers, newspapers taped over windows, “water main breaks” shutting down counting then immediately reopened once Republican observers had departed, etc.)
- Three forms of evidence[iv] backing these claims dovetail perfectly;
- Documentation of extraordinary privileges Dominion provides administrators;
- Affidavits describing voters’ and workers’ experiences that match exactly what they would experience in precincts being gooned by the measures I describe;[v]
- Data (such as that below)[vi] expressing outrageous statistical oddities (e.g., strings of thousands of sequential Biden votes that occur with quadrillion-to-1 improbability, ballot processing velocity spikes that were physically impossible given available site equipment) that coincide with windows of intense intimidation of and interference with those observing the voting and counting.
- In each of several swing states Biden achieved a come-from-behind victory with a margin in the tens-of-thousands of votes thanks to getting hundreds of thousands of votes through these measures.

Conclusion: Election 2020 is an egg that can’t be unscrambled, it must be rejected.
Lawyer for Sidney Powell to Smartmatic: ‘File Your Lawsuit’
- Dominions machines have glaring design flaws making them vulnerable to hacking. The machines have a slot on their motherboards that should be sealed with glue, but instead is left open: anyone with physical access to the machines can slide in the right chip for a few seconds, and that machine is thereafter completely compromised. In addition, there are R232 ports which would allow someone who accesses that port to connect and get root-level access to the machine without a password.
- Dominion’s uses solarwinds network software. On December 13, the US government pulled solarwinds off all federal networks due to its massive security vulnerabilities.
- Dominion’s servers are widely infected with QSnatch malware (see “CISA says 62,000 QNAP NAS devices have been infected with the QSnatch malware”, ZDNet, July 27, 2020). As poll-workers (e.g., administrators) log-in, QSnatch steals their credentials. Thus not only can administrators override (with no audit trail) election security in a precinct, so can anyone who steals those credentials (which, given the ubiquity of QSnatch on Dominion servers, happens everywhere). Dominion sends out software patches that continuously (deliberately?) allow QSnatch to beat their patches.
- Dominion uses SolarWinds networking software. On December 13, the federal government issued an emergency directive to all federal agencies to mitigate the profound network compromises brought by SolarWinds:

In a 2006 New York Times article (“U.S. Investigates Voting Machines’ Venezuela Ties”), Brad Golden wrote:
“The federal government is investigating the takeover last year of a leading American manufacturer of electronic voting systems by a small software company that has been linked to the leftist Venezuelan government of President Hugo Chávez. The inquiry is focusing on the Venezuelan owners of the software company, the Smartmatic Corporation, and is trying to determine whether the government in Caracas has any control or influence over the firm’s operations…” [George Soros Does] The article is a real piece of work selling Soros as a hero, but you’ll get the idea of influence.

- Convicted Felon & Operative For British Monarchy – George Soros : United States Republic Enemy #1
- In 2008, VoterAction (an activist group based in Massachusetts and Washington State) issued a public report (“SEQUOIA VOTING SYSTEMS, INC. USES VOTE-COUNTING SOFTWARE DEVELOPED, OWNED, AND LICENSED BY FOREIGN-OWNED SMARTMATIC, A COMPANY LINKED TO THE VENEZUELAN GOVERNMENT OF HUGO CHÁVEZ”) where they noted:
“U.S. national security is potentially at risk because software used to count votes in 20% of the country during U.S. elections is owned and controlled by a Venezuelan-run company with ties to the Venezuelan government of Hugo Chávez,
1 which has been described as ‘the foremost meddler in foreign elections in the Western hemisphere.’
2 Foreign-owned and foreign-run Smartmatic’s control over vote counting software used in the voting machines of Sequoia Voting Systems… presents a potential national security risk now just as it did in 2006 when the U.S. Committee on Foreign Investment in the United States (“CFIUS”) opened an investigation of Smartmatic’s ownership of Sequoia.
3 CFIUS is a U.S. government inter-agency committee led by the U.S. Department of Treasury that addresses national security risks posed by foreign ownership of or influence over U.S. business, including companies providing the means by which voters in the U.S. elect their President and Congressional Representatives.
4 Rather than answer to CFIUS regarding the ultimate owners of the Smartmatic conglomerate
5 and its ties to the Chávez government, an investment group led by Sequoia management reportedly bought Sequoia from Smartmatic in late 2007 under terms that were not made public.
6 Since then, however, it has come to light that Smartmatic continues to own the software that counts the votes on Sequoia voting machines and licenses to Sequoia that software, which Smartmatic develops in Venezuela.
7 Concern, now, is that Smartmatic’s sale of Sequoia “was fraudulent”,
8 “a sham transaction designed to fool regulators.”
9 Efforts to date have not succeeded in determining the ultimate owners of Smartmatic or the extent to which Smartmatic and the Chávez government of Venezuela have influence over U.S. elections through Smartmatic’s control of the software that counts votes for Sequoia voting machines…”

See also this 2015 Philippines TV interview where Smartmatic’s chairman Mark Malloch-Brown (who, oddly enough, also serves as Vice-Chairman of George Soros’s investment fund and Open Society Institute) initially danced around such Venezuelan connections (note his oh-so-careful parsing of words in this regard) before eventually acknowledging a licensing arrangement between Dominion and Smartmartic.
[iii] Atlanta, Philadelphia, Detroit, Milwaukee, Maricopa County Arizona (Greater Phoenix), Clark County Nevada (Greater Las Vegas).
[iv] Due to my impatience waiting for these facts to bubble up through legal proceedings, and due to the extraordinary nature of the circumstances, I felt it was appropriate to create on article and get it live as soon as possible in order to make the Big Picture available to the public, then add charts and links and other evidence as time and opportunity allowed. As a result, I first posted this essay on the evening of Monday, November 23 and since then have been adducing further evidence since then. That way there will be one article that both tells the story succinctly, yet also gathers in one place much detail backing my claims.
[v] By way of example: Sharpie/Bic switcheroos experienced in Maricopa precincts reflect a wish to generate a large pool of “adjudicated ballots” for administrators, who could drag-and-drop them later to Candidate Biden.

ARIZONA

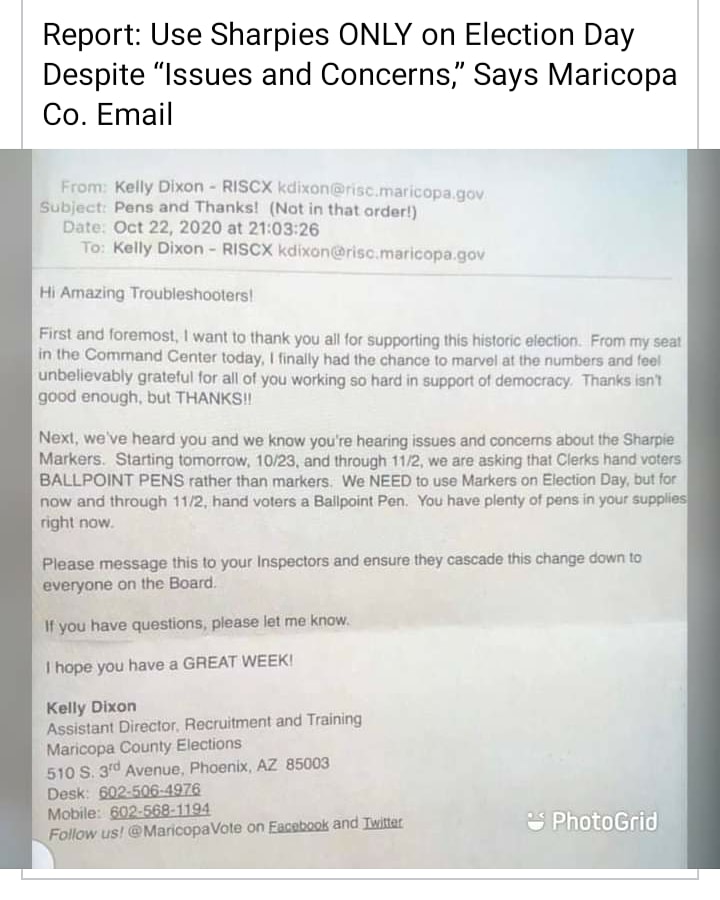
October 22 Maricopa County election official: “…we’ve heard you and we know you’re hearing issues and concerns about the Sharpie Markers. We NEED to use Markrs on Election Day, but for now and through 11/2 hand voters a Ballpoint Pen. You have plenty of pens in your supplies right now…Please message this to your inspectors and ensure they cascade this change down to everyone on the Board…”
GEORGIA




Election officials in Georgia have a history of quickly wiping their tracks: “APNewsBreak: Georgia election server wiped after suit filed” (AP, 10/2017).
Download this fine, heavily-documented affidavit from a Military intelligence analyst concerning Chinese, Iranian, and Russian penetration of Dominion Voting:Download

Related News:
- Forensic analysis: More than 790,000 votes were “laundered” in Arizona
- CORPORATE MEDIA, GOVERNORS HAVE NO STANDING IN U.S. ELECTIONS
- Georgia senators declare that vote fraud in their state was part of a coordinated, illegal scheme to rig the election
- 2012 US PRESIDENTIAL ELECTION FRAUD IN MOTION: OBAMA SENDS “VOTING SERVICES” TO GEORGE SOROS COMPANY IN SPAIN!
- DEMOCRAT OFFICIALS FOUND GUILTY OF ELECTION FRAUD: FORGED PRESIDENTIAL PRIMARY BALLOT IN INDIANA IN 2008 ELECTIONS.
- Evaluations show Texas officials had concerns about Dominion Voting Systems product’s efficiency and reliability when they rejected their use in January of this year.
Remember?
- How To Win An Election Page
- ANOTHER DEEP STATE DEMOCRAT GOES TO PRISON FOR VOTER FRAUD
- CONNECTICUT DEMOCRAT STATE REPRESENTATIVE ARRESTED ON 19 COUNTS OF VOTER FRAUD
- OBAMA’S NAZI UNIONISM: ACORN BRASS, UNION ORGANIZERS DIVIDE $10 MIL RETIREMENT FUND
- RELEASED: OBAMA GAVE ACORN $3 BILLION USD IN TAXPAYER STIMULUS ~ WHILE SHUTTING DOWN AMERICA’S OIL PRODUCTION!
- OBAMA COVERTLY USES TAXPAYER FUNDS THRU ACORN, TO FINANCE SOCIALIST ANTI GUN AGENDA: STOP ACORN TAXPAYER FUNDING NOW!
- WEEKEND REFLECTIONS: OBAMA’S ACORN COMMUNITY ORGANIZERS – BUSTED HELPING PIMP AND PROSTITUTE OBTAIN ILLEGAL LOANS USING AMERICA’S STIMULUS IN ORDER TO ESTABLISH A BROTHEL FOR YOUNG GIRLS FROM EL SALVADOR.

